Classification of different kinds of Hackers
Hacking can be defined as the process of ascertaining and the subsequent
exploitation of the various shortfalls and weaknesses in a computer system or a network of such
computer systems. This exploitation may take the form of accessing and stealing of information,
altering the configuration, changing the structural picture of the computer system and so on.
There are people who hack a system as a sign of protest against the authority. Instead of being vocal
against the policies which they consider unreasonable, they burrow into the technological network
systems employed by the authority and wreak havoc.
Classification – Various kinds
White hat hackers
The term white hat is used to refer to someone who hacks into a computer system or network for
intentions that are not mala fide. They may do as a part of a series of tests performed to check the
efficacy of their security systems or as a part of research and development that is carried out by
companies that manufacture computer security software.
"Also known as ethical hackers, they carry out vulnerability assessments and penetration tests"Black hat hackers
A black hat hacker, as the name suggests is the polar opposite of a white hat hacker in terms of both
intention as well as methodology. They violate a network for mala fide intentions for monetary and
personal gains. They are the illegal communities who fit the commonly perceived stereotype of
computer criminals.
They gain access into a system and steal or destroy the information or modify the same. They may
tweak the program in such a way that it is rendered useless for the intended users. When they notice a
weak spot or vulnerable area in the system, they take control of the system by way of such weak spot.
They keep the proprietors, authorities and the general public in the blind regarding such vulnerability.
They do not make any attempts to fix the lacunae unless their reign faces a threat from a third party.
Grey hat hackers
A grey hat hacker has a curious mix of both black hat and white hat characteristics. He trawls the
internet and sniffs out network faults and hacks into the system. He does so with the sole intention of
demonstrating to the system administrators that their network has a defect in terms of security. Once
hacked into the system, they may offer to diagnose and rectify the defect for a suitable consideration.
Blue hat hackers
These are freelancers who offer their expertise for hire to computer security firms. Before a new
system is introduced in the market, the services of blue hats are called for, to check the system for any potential weaknesses.
Elite hackers
These are the crème de la crème of the hacking community. This is a marker of social status used to
demote the most proficient hackers. They are the first ones to break into a seemingly impenetrable
system and write programs to do so. The elite status is usually conferred on them by the hacking
community to which they belong.
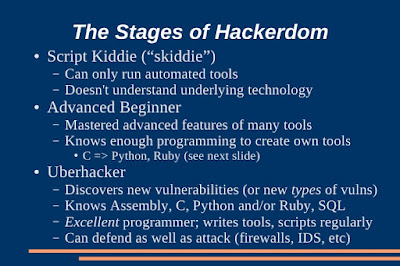
Skiddie
The term "skiddie" is short for "Script Kiddie". These are the amateur level hackers who manage to
break into and access systems by making use of programs written by other expert level hackers. They
have little or no grasp on the intricacies of the program which they use.
Newbie
Newbies, as the name suggests, are hackers who are beginners in the world of hacking, with no prior
experience or knowledge behind them. They hang around at the fringe of the community with the
object of learning the ropes of the trade from their peers.
Hacktivism
This is another version of hacking, in which the individual or the community makes use of their skills
to promulgate any religious or social message through the systems they hack into. Hacktivism can
broadly be classified into two kinds- Cyber terrorism and Right to information. Cyber terrorism
refers to activities that involve breaking into a system with the sole intention of damaging or
destroying it. Such hackers sabotage the operations of the system and render it useless.
The hackers who belong to the "Right to information" category operate with the intention of gathering confidential information from private and public sources and disseminate the same on the public domain.
Intelligence agencies
Intelligence agencies and anti-cyber terrorism departments of various countries also engage in
hacking in order to protect the state interests and to safeguard their national systems against any
foreign threats. Though this cannot be considered as hacking in the true sense of the term, such
agencies engage the services of blue hat hackers as a sort of defense strategy.
Organized crime
This can be construed as a kind of conglomerate of black hat hackers working for a common goal or
under a leadership. They access the systems of government authorities and private organizations to
aid the criminal objectives of the gang to which they belong to.































No comments:
Post a Comment